How to securely transfer files via ssh using scp command under Linux
Feb 09, 2024 pm 01:39 PM
On Unix or Linux operating systems, the scp utility (secure copy) is similar to the more famous command cp, but is used to copy between hosts over a secure and encrypted network. Transfer files and directories between
Since it relies on ssh for data transfer, it provides the same security and uses the same authentication as ssh. Unlike rcp, the scp command will prompt you for a password for authentication if required.
In this article, we will delve into secure file transfer in Linux and learn how to use the scp command. With detailed explanations and example use cases of common scp switches and options, you'll learn how to use this utility.
It’s important to know the following before you start
- Since scp relies on ssh for data transfer, an ssh key or password is required to authenticate on the remote system (Linux file transfer ssh).
- Confirm that you have write permissions on the target system and read permissions on the source file.
- Note: The scp tool uses a colon (:) to differentiate between remote and local locations.
- When copying a file with the same location and name on both sides, scp will overwrite the file without prior warning.
SCP Linux command syntax
In order to start using the scp command, you need to understand its basic syntax, which is in the following format:
less復(fù)制代碼 scp?[OPTION]?[user@]SRC_HOST:]file1?[user@]DEST_HOST:]file2
Options: Represents scp options such as ssh configuration, password, restrictions, ssh port, recursive copy, etc.
[user@]SRC_HOST:]file1: Indicates the source file.
[user@]DEST_HOST:]file2: represents the target file
Like any other command, the scp tool has some options for controlling its behavior. The most common are the following:
- -P: Indicates the ssh port of the remote host to connect to.
- -p: Specifies to preserve file modifications, mode and access time from the original file.
- -q: Need to suppress non-error messages and progress meters.
- -C: Force scp to compress data when passing the -C flag to ssh to enable compression on encrypted secure connections.
- -r: Tells the scp command to copy the entire directory recursively.
- -S: The name of the program used to encrypt the connection. Since ssh is used, the program must understand the ssh switch.
- -v: Verbose mode. Enables scp and ssh to output messages about their progress. This is useful when debugging connection, configuration and authentication issues.
Transfer local files to remote destination
Before we start using scp, let us use cp to copy files from one folder to another. We all know how to use the cp command to achieve this:
bash復(fù)制代碼 cp?/home/linuxmi/linuxmi.mp3?/home/linuxmi/audio
It copies the file linuxmi.mp3 in the home directory of user linuxmi to the home folder of the same user, which is the audio directory of linuxmi.
In a similar manner, an example of the scp command that can be used is as follows:
typescript復(fù)制代碼 scp?/home/linuxmi/linuxmi.mp3?linuxmi@linuxmi.com:/home/linuxmi/audio
Use linuxmi as the login name to upload the linuxmi.mp3 file to the server linuxmicom to the remote directory /home/linuxmi/audio???. Please note that scp will prompt you for the remote password for linuxmi before starting the upload. If no remote directory is provided, the files will be copied to the remote user's home directory. If you don't provide a filename on the destination folder, scp will be made to copy the file with the original name. If you want to save the file under a different name, you need to specify a new file name.
Transfer remote files to local target
In order to download the file, you can mention a remote location as the source location. For example :
scp linuxmi@linuxmi.com:/home/linuxmi/audio/* /home/linuxmi/downloads
It will download all audio files in the remote directory /home/linuxmi/audio on linuxmi.com to the local directory /home/linuxmi/downloads.
Note the file name:
The file name can be composed of user and host to indicate the transfer of the file to or from that host. To avoid scp processing filenames containing ":" as a host specifier, local filenames can be either absolute or relative. However, the remote filename should include both user and host.
Default port number:
If on the remote host, SSH is listening on a different port (i.e. a port other than the default port 22), you can use the -P switch to indicate that port.
Transfer local directory to remote target
Copy a directory to a remote location, similar to copying files. You just need to use the -r flag for recursive transfers.
To copy the entire directory to the remote system, run the command with the -r option, for example:
scp -r /home/linuxmi/local_folder linuxmi@linuxmi.com:/home/linuxmi/remote_folder
File transfer between two remote systems
The following command will copy the file /folder/linuxmi.mp3 from the remote host linuxmi.com to the directory /folder on the remote host www.linuxmi.com.
scp linuxmi@linuxmi.com:/folder/linuxmi.mp3 linuxmi@www.linuxmi.com:/anotherfolder
After initiating this operation, you will be asked to provide the passwords for both remote targets.
In order to route traffic through the local host (i.e. the computer on which the command is executed), use the -3 switch as follows:
scp -3 linuxmi@linuxmi.com:/folder/linuxmi.mp3 linuxmi@www.linuxmi.com:/anotherfolder
The above is the detailed content of How to securely transfer files via ssh using scp command under Linux. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
 How to install Linux alongside Windows (dual boot)?
Jun 18, 2025 am 12:19 AM
How to install Linux alongside Windows (dual boot)?
Jun 18, 2025 am 12:19 AM
The key to installing dual systems in Linux and Windows is partitioning and boot settings. 1. Preparation includes backing up data and compressing existing partitions to make space; 2. Use Ventoy or Rufus to make Linux boot USB disk, recommend Ubuntu; 3. Select "Coexist with other systems" or manually partition during installation (/at least 20GB, /home remaining space, swap optional); 4. Check the installation of third-party drivers to avoid hardware problems; 5. If you do not enter the Grub boot menu after installation, you can use boot-repair to repair the boot or adjust the BIOS startup sequence. As long as the steps are clear and the operation is done properly, the whole process is not complicated.
 How to choose a Linux distro for a beginner?
Jun 19, 2025 am 12:09 AM
How to choose a Linux distro for a beginner?
Jun 19, 2025 am 12:09 AM
Newbie users should first clarify their usage requirements when choosing a Linux distribution. 1. Choose Ubuntu or LinuxMint for daily use; programming and development are suitable for Manjaro or Fedora; use Lubuntu and other lightweight systems for old devices; recommend CentOSStream or Debian to learn the underlying principles. 2. Stability is preferred for UbuntuLTS or Debian; you can choose Arch or Manjaro to pursue new features. 3. In terms of community support, Ubuntu and LinuxMint are rich in resources, and Arch documents are technically oriented. 4. In terms of installation difficulty, Ubuntu and LinuxMint are relatively simple, and Arch is suitable for those with basic needs. It is recommended to try it first and then decide.
 How to add a new disk to Linux
Jun 27, 2025 am 12:15 AM
How to add a new disk to Linux
Jun 27, 2025 am 12:15 AM
The steps to add a new hard disk to the Linux system are as follows: 1. Confirm that the hard disk is recognized and use lsblk or fdisk-l to check; 2. Use fdisk or parted partitions, such as fdisk/dev/sdb and create and save; 3. Format the partition to a file system, such as mkfs.ext4/dev/sdb1; 4. Use the mount command for temporary mounts, such as mount/dev/sdb1/mnt/data; 5. Modify /etc/fstab to achieve automatic mount on the computer, and test the mount first to ensure correctness. Be sure to confirm data security before operation to avoid hardware connection problems.
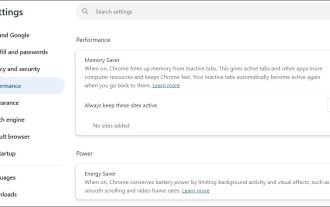 Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Have problems uploading files in Google Chrome? This may be annoying, right? Whether you are attaching documents to emails, sharing images on social media, or submitting important files for work or school, a smooth file upload process is crucial. So, it can be frustrating if your file uploads continue to fail in Chrome on Windows PC. If you're not ready to give up your favorite browser, here are some tips for fixes that can't upload files on Windows Google Chrome 1. Start with Universal Repair Before we learn about any advanced troubleshooting tips, it's best to try some of the basic solutions mentioned below. Troubleshooting Internet connection issues: Internet connection
 Where are system logs located in Linux?
Jun 24, 2025 am 12:15 AM
Where are system logs located in Linux?
Jun 24, 2025 am 12:15 AM
Logs in Linux systems are usually stored in the /var/log directory, which contains a variety of key log files, such as syslog or messages (record system logs), auth.log (record authentication events), kern.log (record kernel messages), dpkg.log or yum.log (record package operations), boot.log (record startup information); log content can be viewed through cat, tail-f or journalctl commands; application logs are often located in subdirectories under /var/log, such as Apache's apache2 or httpd directory, MySQL log files, etc.; at the same time, it is necessary to note that log permissions usually require s
 What is the sudo command and when should I use it?
Jul 02, 2025 am 12:20 AM
What is the sudo command and when should I use it?
Jul 02, 2025 am 12:20 AM
sudo stands for "substituteuserdo" or "superuserdo", allowing users to run commands with permissions of other users (usually root). Its core uses include: 1. Perform system-level operations such as installing software or editing system files; 2. Accessing protected directories or logs; 3. Manage services such as restarting nginx; 4. Modify global settings such as /etc/hosts. When using it, the system will check the /etc/sudoers configuration and verify the user password, provide temporary permissions instead of continuously logging in as root, ensuring security. Best practices include: only when necessary, avoid blindly executing network commands, editing sudoers files with visudo, and considering continuous operations.
 How to manage groups on Linux
Jul 06, 2025 am 12:02 AM
How to manage groups on Linux
Jul 06, 2025 am 12:02 AM
To manage Linux user groups, you need to master the operation of viewing, creating, deleting, modifying, and user attribute adjustment. To view user group information, you can use cat/etc/group or getentgroup, use groups [username] or id [username] to view the group to which the user belongs; use groupadd to create a group, and use groupdel to specify the GID; use groupdel to delete empty groups; use usermod-aG to add users to the group, and use usermod-g to modify the main group; use usermod-g to remove users from the group by editing /etc/group or using the vigr command; use groupmod-n (change name) or groupmod-g (change GID) to modify group properties, and remember to update the permissions of relevant files.
 How to find my private and public IP address in Linux?
Jul 09, 2025 am 12:37 AM
How to find my private and public IP address in Linux?
Jul 09, 2025 am 12:37 AM
In Linux systems, 1. Use ipa or hostname-I command to view private IP; 2. Use curlifconfig.me or curlipinfo.io/ip to obtain public IP; 3. The desktop version can view private IP through system settings, and the browser can access specific websites to view public IP; 4. Common commands can be set as aliases for quick call. These methods are simple and practical, suitable for IP viewing needs in different scenarios.






