 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to handle and respond to security threats in Linux servers
How to handle and respond to security threats in Linux servers
How to handle and respond to security threats in Linux servers
Sep 11, 2023 am 10:10 AM
How to deal with and respond to security threats in Linux servers
With the development of the Internet, server security has become an important issue that enterprises and individuals must face. Linux servers, in particular, have become the main target of hacker attacks due to their open source nature and wide application. In order to protect the server from security threats, we need to take a series of measures to ensure the security of the server. This article will introduce some common Linux server security threats and how to deal with them.
First, we need to understand common Linux server security threats. Here are some common security threats:
- Remote login attacks: Hackers remotely log into servers by guessing passwords or running phishing attacks.
- Denial of service attack: Hackers use a large number of requests to occupy server resources, causing the server to crash.
- Trojan horses and backdoors: Hackers can remotely control servers without authorization by implanting Trojan horses or backdoor programs.
- System vulnerability exploitation: Hackers gain system privileges by exploiting vulnerabilities in the operating system or software.
- Data leakage: Hackers steal sensitive data from the server, causing personal information to be leaked.
Next, we will introduce some methods to deal with and respond to these security threats:
- Use a strong password policy: Make sure the login password for the server is strong enough, including numbers, letters and special characters, and change your password regularly. In addition, you can try to use the public key-private key authentication method to avoid password login.
- Update and upgrade software regularly: Install security patches for operating systems and software in a timely manner to fix known vulnerabilities and defects.
- Firewall settings: Configure and enable the firewall to limit unnecessary inbound and outbound traffic. You can use tools such as iptables or ufw to set up the firewall.
- Install and configure an intrusion detection system (IDS): IDS can monitor network activities on the server and detect potential attacks. Common IDS include Snort and Suricata, etc.
- Configure security updates and logging: Ensure server configuration files are backed up and updated regularly, and log all activity on the server to find and track security events.
- Back up data regularly: Back up important data on the server regularly to prevent data loss or attacks. Backup data should be saved on a different server or offline storage media.
- Use secure encryption protocols: Ensure that all communication traffic with the server is encrypted by using secure communication protocols (such as SSH and HTTPS, etc.).
- Block unused services and ports: Close unused services and ports on the server to reduce the attack surface.
- Use security software: Install and configure security software (such as anti-virus software, intrusion detection systems, firewalls, etc.) to provide additional protection.
- Train employees and build security awareness: Regularly train employees on best practices for server security and the latest security threats to improve employee security awareness.
Finally, maintaining security awareness and continuous monitoring are important parts of handling and responding to Linux server security threats. Security threats are constantly changing, and we need to always pay attention to the latest threats and security patches, as well as monitor server activities and logs to discover and respond to potential security issues in a timely manner.
In short, the security threats of Linux servers cannot be ignored, and we need to take a series of measures to protect the security of the servers. Server security can be improved by using strong password policies, updating and upgrading software, configuring firewalls and intrusion detection systems, and more. At the same time, continuous security awareness building and monitoring work are also indispensable. Only by taking comprehensive security measures can we better respond to and deal with security threats in Linux servers.
The above is the detailed content of How to handle and respond to security threats in Linux servers. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undress AI Tool
Undress images for free

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)
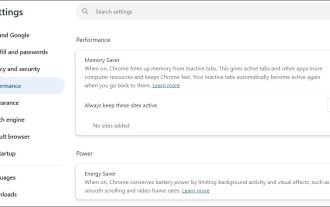 Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Fixed the failure to upload files in Windows Google Chrome
Jul 08, 2025 pm 02:33 PM
Have problems uploading files in Google Chrome? This may be annoying, right? Whether you are attaching documents to emails, sharing images on social media, or submitting important files for work or school, a smooth file upload process is crucial. So, it can be frustrating if your file uploads continue to fail in Chrome on Windows PC. If you're not ready to give up your favorite browser, here are some tips for fixes that can't upload files on Windows Google Chrome 1. Start with Universal Repair Before we learn about any advanced troubleshooting tips, it's best to try some of the basic solutions mentioned below. Troubleshooting Internet connection issues: Internet connection
 How to manage groups on Linux
Jul 06, 2025 am 12:02 AM
How to manage groups on Linux
Jul 06, 2025 am 12:02 AM
To manage Linux user groups, you need to master the operation of viewing, creating, deleting, modifying, and user attribute adjustment. To view user group information, you can use cat/etc/group or getentgroup, use groups [username] or id [username] to view the group to which the user belongs; use groupadd to create a group, and use groupdel to specify the GID; use groupdel to delete empty groups; use usermod-aG to add users to the group, and use usermod-g to modify the main group; use usermod-g to remove users from the group by editing /etc/group or using the vigr command; use groupmod-n (change name) or groupmod-g (change GID) to modify group properties, and remember to update the permissions of relevant files.
 How to find my private and public IP address in Linux?
Jul 09, 2025 am 12:37 AM
How to find my private and public IP address in Linux?
Jul 09, 2025 am 12:37 AM
In Linux systems, 1. Use ipa or hostname-I command to view private IP; 2. Use curlifconfig.me or curlipinfo.io/ip to obtain public IP; 3. The desktop version can view private IP through system settings, and the browser can access specific websites to view public IP; 4. Common commands can be set as aliases for quick call. These methods are simple and practical, suitable for IP viewing needs in different scenarios.
 What is the code number of Bitcoin? What style of code is Bitcoin?
Jul 22, 2025 pm 09:51 PM
What is the code number of Bitcoin? What style of code is Bitcoin?
Jul 22, 2025 pm 09:51 PM
As a pioneer in the digital world, Bitcoin’s unique code name and underlying technology have always been the focus of people’s attention. Its standard code is BTC, also known as XBT on certain platforms that meet international standards. From a technical point of view, Bitcoin is not a single code style, but a huge and sophisticated open source software project. Its core code is mainly written in C and incorporates cryptography, distributed systems and economics principles, so that anyone can view, review and contribute its code.
 System requirements to install linux
Jul 20, 2025 am 03:49 AM
System requirements to install linux
Jul 20, 2025 am 03:49 AM
Linuxcanrunonmodesthardwarewithspecificminimumrequirements.A1GHzprocessor(x86orx86_64)isneeded,withadual-coreCPUrecommended.RAMshouldbeatleast512MBforcommand-lineuseor2GBfordesktopenvironments.Diskspacerequiresaminimumof5–10GB,though25GBisbetterforad
 How to make PHP container support automatic construction? Continuously integrated CI configuration method of PHP environment
Jul 25, 2025 pm 08:54 PM
How to make PHP container support automatic construction? Continuously integrated CI configuration method of PHP environment
Jul 25, 2025 pm 08:54 PM
To enable PHP containers to support automatic construction, the core lies in configuring the continuous integration (CI) process. 1. Use Dockerfile to define the PHP environment, including basic image, extension installation, dependency management and permission settings; 2. Configure CI/CD tools such as GitLabCI, and define the build, test and deployment stages through the .gitlab-ci.yml file to achieve automatic construction, testing and deployment; 3. Integrate test frameworks such as PHPUnit to ensure that tests are automatically run after code changes; 4. Use automated deployment strategies such as Kubernetes to define deployment configuration through the deployment.yaml file; 5. Optimize Dockerfile and adopt multi-stage construction
 How to use the `shutdown` command
Jul 15, 2025 am 12:26 AM
How to use the `shutdown` command
Jul 15, 2025 am 12:26 AM
The shutdown command of Linux/macOS can be shut down, restarted, and timed operations through parameters. 1. Turn off the machine immediately and use sudoshutdownnow or -h/-P parameters; 2. Use the time or specific time point for the shutdown, cancel the use of -c; 3. Use the -r parameters to restart, support timed restart; 4. Pay attention to the need for sudo permissions, be cautious in remote operation, and avoid data loss.
 How to build an independent PHP task container environment. How to configure the container for running PHP timed scripts
Jul 25, 2025 pm 07:27 PM
How to build an independent PHP task container environment. How to configure the container for running PHP timed scripts
Jul 25, 2025 pm 07:27 PM
Building an independent PHP task container environment can be implemented through Docker. The specific steps are as follows: 1. Install Docker and DockerCompose as the basis; 2. Create an independent directory to store Dockerfile and crontab files; 3. Write Dockerfile to define the PHPCLI environment and install cron and necessary extensions; 4. Write a crontab file to define timing tasks; 5. Write a docker-compose.yml mount script directory and configure environment variables; 6. Start the container and verify the log. Compared with performing timing tasks in web containers, independent containers have the advantages of resource isolation, pure environment, strong stability, and easy expansion. To ensure logging and error capture





